Why Web Application Penetration Testing Still...
Web applications remain one of the most targeted attack surfaces for modern organizations. Despite a...

Web applications remain one of the most targeted attack surfaces for modern organizations. Despite a...
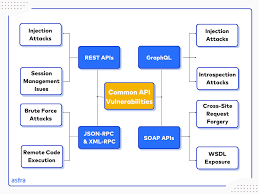
Broken Access Control remains one of the most critical and commonly exploited vulnerabilities in mod...
Cloud environments offer scalability and flexibility, but misconfigurations remain one of the leadin...
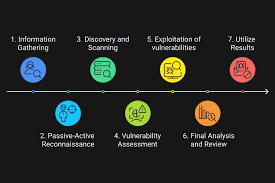
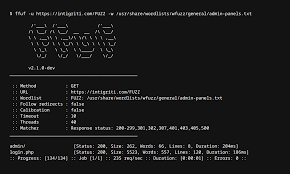
A successful penetration test is not about running tools randomly—it follows a structured workflow t...
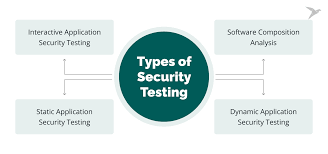
Automated security scanners play an important role in identifying common vulnerabilities at scale, b...
Vulnerability research is a disciplined process that goes beyond finding security flaws—it focuses o...