Manual vs Automated Testing: Why Human-Led Penetration Testing Still Wins
Automated security scanners play an important role in identifying common vulnerabilities at scale, but they are not a replacement for skilled human-led penetration testing. Many of the most impactful security issues today are discovered through manual testing that focuses on logic, context, and real-world attack behavior.
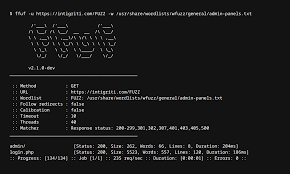
Automated tools are effective at detecting known patterns such as missing headers, outdated components, and basic injection flaws. However, they often struggle with vulnerabilities that require understanding application workflows, business logic, and authorization boundaries. Issues such as IDOR, broken access control, privilege escalation, and logic flaws are frequently missed by scanners.
Manual penetration testing involves actively interacting with the application as an attacker would. This includes manipulating parameters, chaining low-severity issues into high-impact exploits, and testing how systems behave under unexpected conditions. In bug bounty programs, these human-driven techniques are often responsible for the highest-paying findings.
Another key advantage of manual testing is contextual risk assessment. A scanner may flag dozens of low-risk findings, but a penetration tester can identify which vulnerabilities actually pose a threat to the business and demonstrate real impact through controlled exploitation.
The most effective security programs combine both approaches. Automated tools provide coverage and efficiency, while manual testing delivers depth, creativity, and accurate risk validation. Regular penetration testing ensures that organizations are protected not only from known vulnerabilities but also from emerging attack techniques that automation alone cannot detect.
In an evolving threat landscape, human expertise remains a critical component of effective offensive security and vulnerability discovery.