Why Web Application Penetration Testing Still...
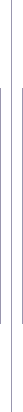
Web applications remain one of the most targeted attack surfaces for modern organizations. Despite a...

Penetration Tester
Application Security Specialist
Cloud Security Tester
I am a Web, Network, and Cloud Penetration Tester focused on identifying real-world security risks before attackers exploit them. I approach security from an adversarial mindset—combining manual testing, industry frameworks, and practical exploitation techniques to uncover vulnerabilities across applications, APIs, networks, and cloud environments.
My work emphasizes clarity and impact: translating technical findings into actionable remediation guidance aligned with OWASP Top 10, PTES, and MITRE ATT&CK. I collaborate closely with stakeholders to improve security posture, reduce attack surface, and strengthen defensive controls.
My skill set spans offensive security testing, cloud security analysis, and professional reporting. I apply structured methodologies and hands-on techniques to deliver meaningful, risk-focused security assessments.
Completed hands-on cybersecurity and ethical hacking training focused on penetration testing, vulnerability assessment, and web, network, and cloud security fundamentals, using industry-standard tools and methodologies.
Hands-on penetration testing experience across web, network, API, and cloud environments, including AWS security assessments, vulnerability analysis, reporting, and incident response simulations.
Completed a virtual cybersecurity job simulation covering penetration testing, security frameworks, reporting, lab configuration, and vulnerability management workflows.
Structured cybersecurity and ethical hacking training with hands-on experience in reconnaissance, exploitation, and core Linux, networking, and security fundamentals.
Web applications remain one of the most targeted attack surfaces for modern organizations. Despite a...
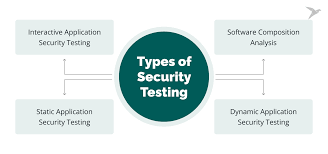
Broken Access Control remains one of the most critical and commonly exploited vulnerabilities in mod...
Cloud environments offer scalability and flexibility, but misconfigurations remain one of the leadin...