Common AWS Misconfigurations Attackers Actively Exploit
Cloud environments offer scalability and flexibility, but misconfigurations remain one of the leading causes of security breaches. In Amazon Web Services (AWS), a single misconfigured permission or exposed resource can provide attackers with unauthorized access to sensitive data or critical infrastructure.
One of the most common issues observed during cloud security assessments is overly permissive IAM policies. Excessive privileges, wildcard permissions, and unused roles significantly increase the attack surface and enable privilege escalation paths if an account is compromised.
Publicly accessible S3 buckets are another frequent finding. Misconfigured bucket policies or access control lists can expose sensitive files, backups, or logs to the internet. Attackers continuously scan for exposed storage resources and often exploit them within minutes of discovery.
Insecure EC2 configurations also pose risks. Open security groups, unrestricted inbound ports, and weak network segmentation can allow attackers to gain initial access and move laterally within the environment. Combined with insufficient monitoring, these issues may go undetected for extended periods.
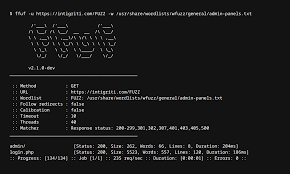
Effective cloud security testing involves both automated and manual techniques. Tools such as ScoutSuite, Prowler, and the AWS CLI help identify misconfigurations at scale, while manual review validates real-world exploitability and business impact.
By performing regular AWS security assessments and aligning configurations with best practices, organizations can significantly reduce the risk of cloud-based attacks. Proactive testing ensures that cloud infrastructure remains resilient against evolving threat techniques.