From Discovery to Disclosure: A Practical Approach to Vulnerability Research
Vulnerability research is a disciplined process that goes beyond finding security flaws—it focuses on understanding root causes, assessing real-world impact, and supporting responsible remediation. Effective research combines technical skill, structured methodology, and ethical disclosure practices.
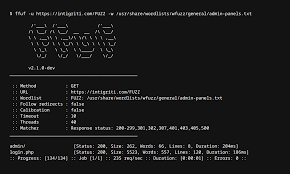
The process typically begins with attack surface analysis and targeted testing. Researchers analyze application behavior, input handling, authentication flows, and access control logic to identify unexpected or insecure functionality. Manual testing plays a critical role at this stage, especially when evaluating business logic and authorization mechanisms.
Once a vulnerability is identified, validation is essential. Researchers confirm exploitability by developing controlled proof-of-concepts that demonstrate impact without causing harm. This step helps distinguish theoretical issues from vulnerabilities that present real risk to users and systems.
Risk assessment follows validation. Using frameworks such as CVSS, vulnerabilities are evaluated based on exploitability, impact, and likelihood. Clear risk scoring allows security teams and stakeholders to prioritize remediation efforts effectively.
Responsible disclosure is a key component of vulnerability research. Findings are documented with detailed technical descriptions, reproduction steps, and remediation recommendations. Clear communication ensures that development and security teams can address the issue efficiently while minimizing exposure.
Vulnerability research contributes directly to stronger security programs. By uncovering weaknesses before they are exploited and supporting responsible remediation, researchers play a vital role in improving application resilience and protecting users from real-world attacks.