Web Application Penetration Test – OWASP Top 10 Assessment
This project involved a full-scope web application penetration test conducted against a simulated production environment. The objective was to identify, validate, and document security vulnerabilities that could lead to unauthorized access, data exposure, or account compromise.
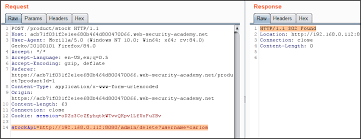
The assessment combined manual testing techniques with targeted automated tooling to uncover vulnerabilities often missed by scanners. Testing followed OWASP Top 10 and PTES methodologies and focused on real-world attacker behavior.
Scope & Activities
-
Authentication and authorization testing
-
Access control validation and IDOR discovery
-
Input validation and injection testing
-
Session management and token handling review
-
Business logic abuse scenarios
Key Findings
-
Broken access control leading to horizontal privilege escalation
-
Reflected XSS due to improper input sanitization
-
Weak session invalidation allowing session reuse
Tools Used
Burp Suite, OWASP ZAP, SQLmap, Gobuster, Firefox DevTools
Outcome
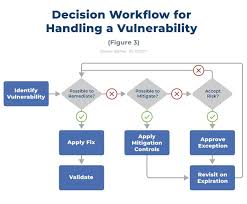
All findings were documented with proof-of-concept evidence, CVSS severity ratings, and clear remediation guidance tailored for developers and security teams.