Why Web Application Penetration Testing Still Matters
Web applications remain one of the most targeted attack surfaces for modern organizations. Despite advances in security tooling and automated scanning, critical vulnerabilities continue to be introduced through insecure design decisions, flawed business logic, and improper access control.
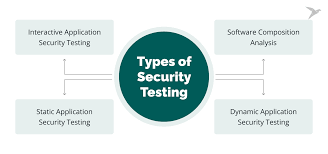
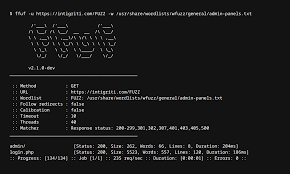
Web application penetration testing goes beyond automated vulnerability scanning. It simulates real-world attacker behavior to identify weaknesses that tools alone often fail to detect. By combining manual testing techniques with industry-standard frameworks, penetration testers can uncover security gaps before they are exploited in production environments.
During a typical web application penetration test, assessments focus on areas such as authentication and authorization mechanisms, session management, input validation, and access control enforcement. Common issues include broken access control, insecure direct object references (IDOR), injection vulnerabilities, cross-site scripting (XSS), and business logic flaws that can lead to unauthorized actions.
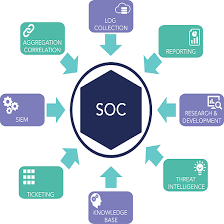
Effective penetration testing follows structured methodologies such as the OWASP Top 10 and PTES while incorporating practical attack scenarios mapped to the MITRE ATT&CK framework. This approach ensures findings are not only technically accurate but also aligned with real-world threat behavior.
Beyond identifying vulnerabilities, the true value of penetration testing lies in clear reporting. Well-documented findings, proof-of-concept evidence, and actionable remediation guidance enable development and security teams to prioritize fixes and strengthen overall application security.
As organizations continue to rely on web applications for critical operations, regular penetration testing remains an essential component of a mature security program. Proactive testing helps reduce risk, improve resilience, and protect both users and business assets.