Understanding IDOR and Broken Access Control in Modern Applications
Broken Access Control remains one of the most critical and commonly exploited vulnerabilities in modern web and API-driven applications. In many real-world breaches, attackers do not rely on complex exploits—they simply access resources they should not be authorized to see.
Insecure Direct Object References (IDOR) occur when an application exposes internal object identifiers, such as user IDs or document numbers, without proper authorization checks. If access control is not enforced on the server side, an attacker can manipulate these identifiers to access or modify data belonging to other users.
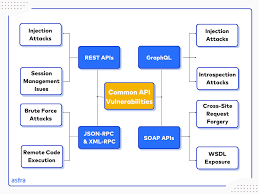
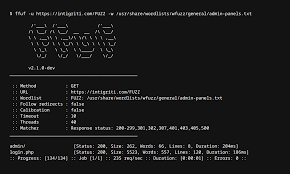
IDOR vulnerabilities are especially prevalent in REST APIs, where predictable endpoints and JSON-based requests make enumeration easier. Common examples include changing a user ID in a request to retrieve another user’s profile, invoices, or sensitive records.
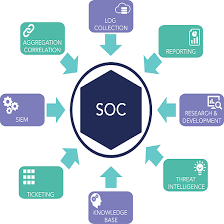
During penetration testing engagements, access control testing involves validating authorization at every function and endpoint. This includes horizontal access control (access between users of the same role) and vertical access control (privilege escalation between roles). Manual testing is essential, as automated scanners often fail to detect logic-based authorization flaws.Effective mitigation of IDOR and broken access control requires enforcing authorization checks on the server side, using indirect object references where possible, and validating permissions at every request—not just during authentication.
By aligning testing efforts with frameworks such as the OWASP Top 10 and OWASP API Security Top 10, organizations can better identify and remediate access control weaknesses before attackers exploit them. Regular penetration testing plays a vital role in uncovering these issues early and strengthening overall application security.