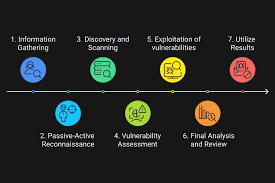
From Reconnaissance to Exploitation: A Practical Penetration Testing Workflow
A successful penetration test is not about running tools randomly—it follows a structured workflow that mirrors how real attackers operate. Understanding this process is essential for identifying meaningful security risks rather than surface-level issues.
The engagement typically begins with reconnaissance and information gathering. This phase focuses on identifying attack surfaces through asset discovery, subdomain enumeration, service fingerprinting, and OSINT. Tools such as Amass, Subfinder, Nmap, and Shodan help map exposed systems and services.
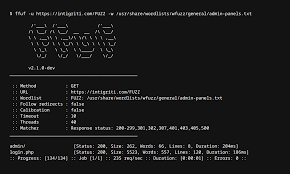
Next is enumeration and vulnerability identification, where discovered services and applications are analyzed for weaknesses. This includes version analysis, authentication testing, access control validation, and manual inspection of application behavior. Automated scanners may assist at this stage, but manual testing is critical to validate findings and uncover logic flaws.
Once vulnerabilities are identified, the tester moves into controlled exploitation. This phase demonstrates real-world impact by safely exploiting issues such as broken access control, IDOR, injection flaws, or misconfigurations. Exploitation is performed responsibly to avoid system disruption while proving risk.
In network and cloud environments, exploitation may lead to privilege escalation and lateral movement, simulating how an attacker could expand access across systems. These activities are often mapped to the MITRE ATT&CK framework to illustrate realistic attack paths and business impact.
The final and most important phase is reporting. A professional penetration test delivers clear documentation, including attack narratives, proof-of-concept evidence, CVSS-based severity ratings, and prioritized remediation guidance. This ensures stakeholders can understand risk and take effective action.
By following a structured penetration testing workflow, organizations gain actionable insight into their security posture and can address vulnerabilities before they are exploited in real-world attacks.