Vulnerability Research & Analysis
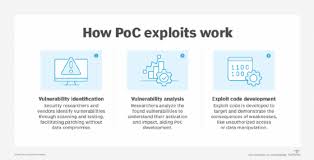
This project focuses on researching, identifying, and validating security vulnerabilities across web applications, APIs, and supporting infrastructure. The work emphasizes understanding root causes, exploitability, and real-world impact rather than relying solely on automated scanning results.
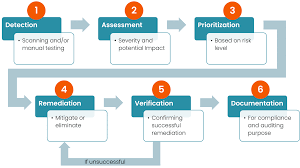
Research activities included manual testing, payload crafting, request manipulation, and review of application logic to uncover issues such as broken access control, injection flaws, and authentication weaknesses. Findings were mapped to OWASP Top 10 and CVSS scoring standards to clearly communicate risk.
Research Scope
-
Manual vulnerability discovery and validation
-
Analysis of false positives from automated tools
-
Exploitability and impact assessment
-
Vulnerability classification using OWASP Top 10
-
CVSS scoring and risk prioritization
Tools & Techniques
Burp Suite, OWASP ZAP, SQLmap, Postman, manual HTTP analysis, custom payloads
Outcome
Each vulnerability was documented with proof-of-concept evidence, impact explanation, and actionable remediation guidance suitable for developers and security teams.