AWS Cloud Security Assessment & Misconfiguration Review
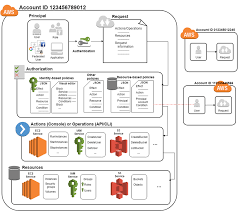
This project focused on assessing the security posture of an Amazon Web Services (AWS) environment to identify misconfigurations, excessive privileges, and exposed cloud resources that could be abused by attackers.
The assessment combined automated tooling with manual validation to simulate real-world cloud attack paths, including privilege escalation and data exposure scenarios. Testing aligned with cloud security best practices and offensive security methodologies.
Scope & Activities
-
IAM user, role, and policy review
-
Privilege escalation path analysis
-
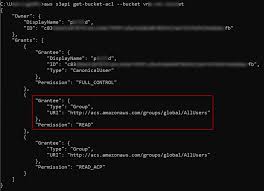
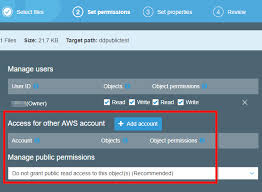
S3 bucket exposure and access control testing
-
EC2 security group and network exposure review
-
Logging and monitoring validation (CloudTrail)
Key Findings
-
Over-permissive IAM policies allowing privilege escalation
-
Publicly accessible S3 buckets exposing sensitive data
-
Excessive inbound security group rules increasing attack surface
Tools Used
ScoutSuite, Prowler, AWS CLI, IAM Policy Simulator
Outcome
All findings were documented with risk severity ratings, attack scenarios, and prioritized remediation steps to reduce cloud exposure and strengthen the overall security posture.